Search
Search for projects by name
 Cartesi Authority Honeypot
Cartesi Authority Honeypot
Badges
About
Honeypot is an application-specific rollup designed to challenge the security of Cartesi Rollups. It provides a gamified battlefield to incentivize bug hunters to hack the application to obtain the funds locked in the rollup contract.
Badges
About
Honeypot is an application-specific rollup designed to challenge the security of Cartesi Rollups. It provides a gamified battlefield to incentivize bug hunters to hack the application to obtain the funds locked in the rollup contract.
Why is the project listed in others?
Consequence: projects without a proper proof system fully rely on single entities to safely update the state. A malicious proposer can finalize an invalid state, which can cause loss of funds.
Learn more about the recategorisation here.
2024 Jul 01 — 2025 Jul 01
The section shows the operating costs that L2s pay to Ethereum.
2024 Jul 02 — 2025 Jun 30
The chart illustrates how "live" the project's operators are by displaying how frequently they submit transactions of the selected type and if these intervals deviate from their typical schedule.
2025 Jun 30 — 30
Funds can be stolen if
Funds can be frozen if
MEV can be extracted if
Currently the system permits invalid state roots. More details in project overview.
All of the data needed for proof construction is published on Ethereum L1.
Users can exit funds at any time because contracts are not upgradeable.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
All transaction data is recorded on chain
All executed transactions are submitted to an on chain smart contract. The execution of the rollup is based entirely on the submitted transactions, so anyone monitoring the contract can know the correct state of the rollup chain.
No compression is used.
The genesis state is derived from the Honeypot Cartesi Machine template, which can be found within the Honeypot server Docker image at /var/opt/cartesi/machine-snapshots/0_0. Alternatively, it is possible to recreate it by following the build procedure outlined in the Honeypot GitHub Repository.
Ultimately, Cartesi DApps will use interactive fraud proofs to enforce state correctness. This feature is currently in development and the Honeypot DApp permits invalid state roots. Since Honeypot is immutable, this feature will not be added to the DApp.
Funds can be stolen if an invalid state root is submitted to the system by the configured Authority (CRITICAL).
The system has a centralized operator
The operator is the only entity that can propose blocks. A live and trustworthy operator is vital to the health of the system.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is settled the funds become available for withdrawal on L1. The process of settling a block usually takes several days to complete. Finally the user submits an L1 transaction to claim the funds.
Funds can be frozen if the centralized validator goes down. Users cannot produce blocks themselves and exiting the system requires new block production (CRITICAL).
Ethereum
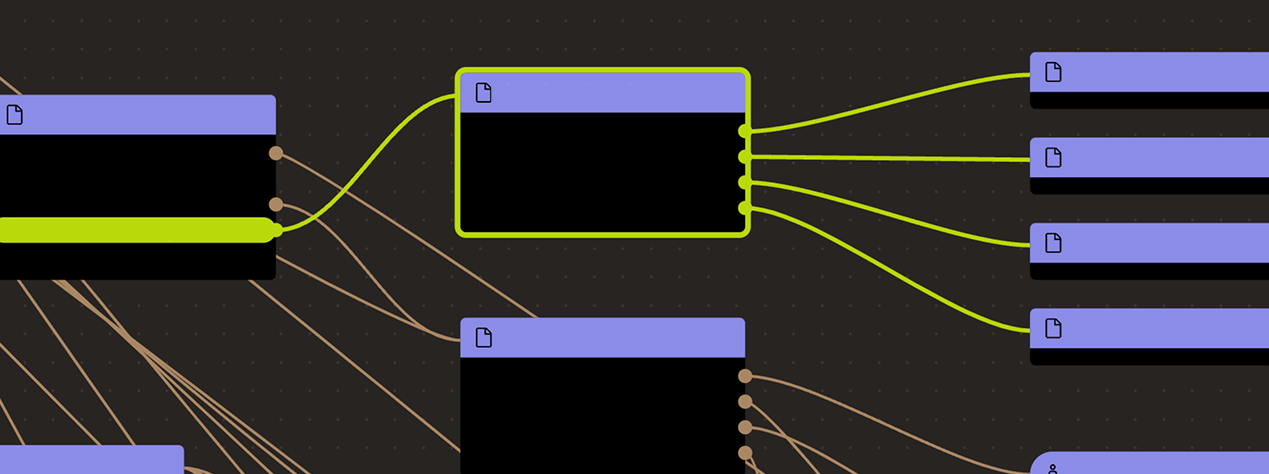
Actors:
The Authority owner can submit claims to the Honeypot DApp.
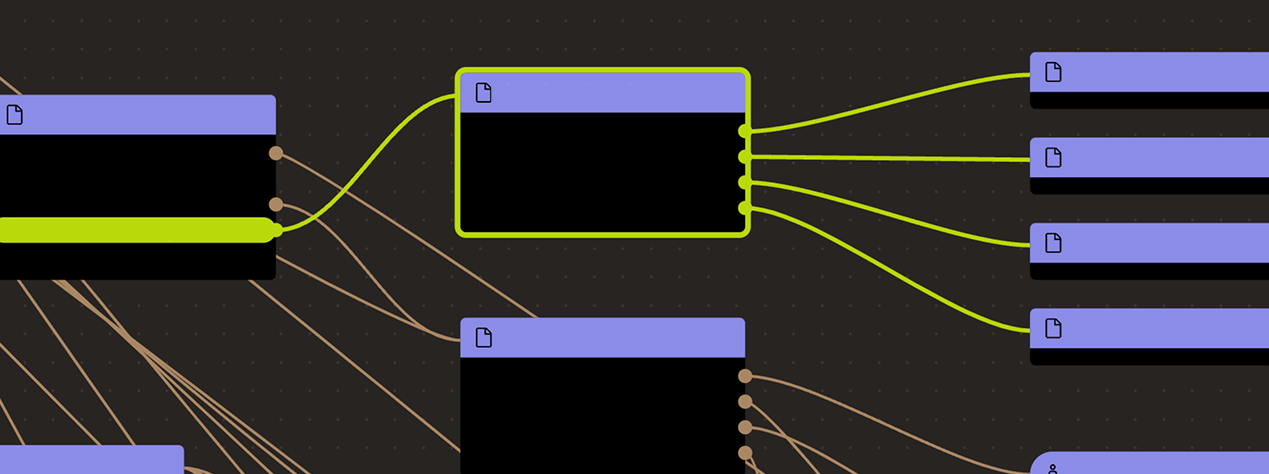
Ethereum
CartesiDApp instance for the Honeypot DApp, responsible for holding assets and allowing the DApp to interact with other smart contracts.
- This contract can store any token.
Contract that receives arbitrary blobs as inputs to Cartesi DApps.
Contract that allows anyone to perform transfers of ERC-20 tokens to Cartesi DApps.
Simple consensus model controlled by a single address, the owner.
Contract that stores claims for Cartesi DApps.
Value Secured is calculated based on these smart contracts and tokens:
Contract storing bounty funds.